Protecting your websites with DNS-Based Authentication of Named Entities (DANE)

Nexusguard

Share to:
How can your users have unwavering confidence that your HTTPS-protected website is precisely what it appears to be—the authentic representation of your site? In today's landscape, your web browser places its trust in Certificate Authorities (CAs), and you, in turn, rely on these trusted entities to issue certificates exclusively to the rightful owners of websites.
Unfortunately, numerous CA providers have faced security breaches in the past, resulting in the issuance of certificates for widely recognized domains to unauthorized individuals who lack ownership of those domains. This raises a crucial question: How can your users ensure that the X.509 certificate offered by your HTTPS server is genuinely intended for this server and not a fraudulent one devised for a malicious man-in-the-middle attack?
This is where DNS-based Authentication of Named Entities (DANE) comes into the picture, adding another layer of security by tying the X.509 certificate of a website to the Domain Name System (DNS). In doing so, it establishes a second independent channel that offers users information to verify the authenticity and legitimacy of the presented X.509 certificate.
What is DANE and the Rationale behind it?
DANE is an Internet security protocol to enable X.509 digital certificates, commonly employed for Transport Layer Security (TLS), to be bound to domain names using Domain Name System Security Extensions (DNSSEC).
As a solution to authenticate TLS client and server entities independently of a CA, the concept of DANE was introduced in RFC 6698. To provide operational and deployment guidance, it was later revised and updated in RFC 7671.
The foundation of TLS encryption currently relies on certificates issued by CAs. However, security breaches in recent years among CAs, resulting in the issuance of certificates to unauthorized entities, raised concerns regarding the trustworthiness of numerous CAs, as a single breached CA could potentially issue certificates for any domain name.

To address these challenges, DANE emerged as a solution, empowering domain name administrators to certify keys utilized in TLS clients or servers within their domain by securely storing them in the Domain Name System (DNS). To ensure the effectiveness of its security model, DANE requires the DNS records to be signed with DNSSEC, enhancing the overall integrity and reliability of the system.
Leveraging the DNS infrastructure, DANE allows the binding of X.509 digital certificates directly to domain names, ensuring that the certificate presented by a server or client is specifically associated with the domain being accessed.
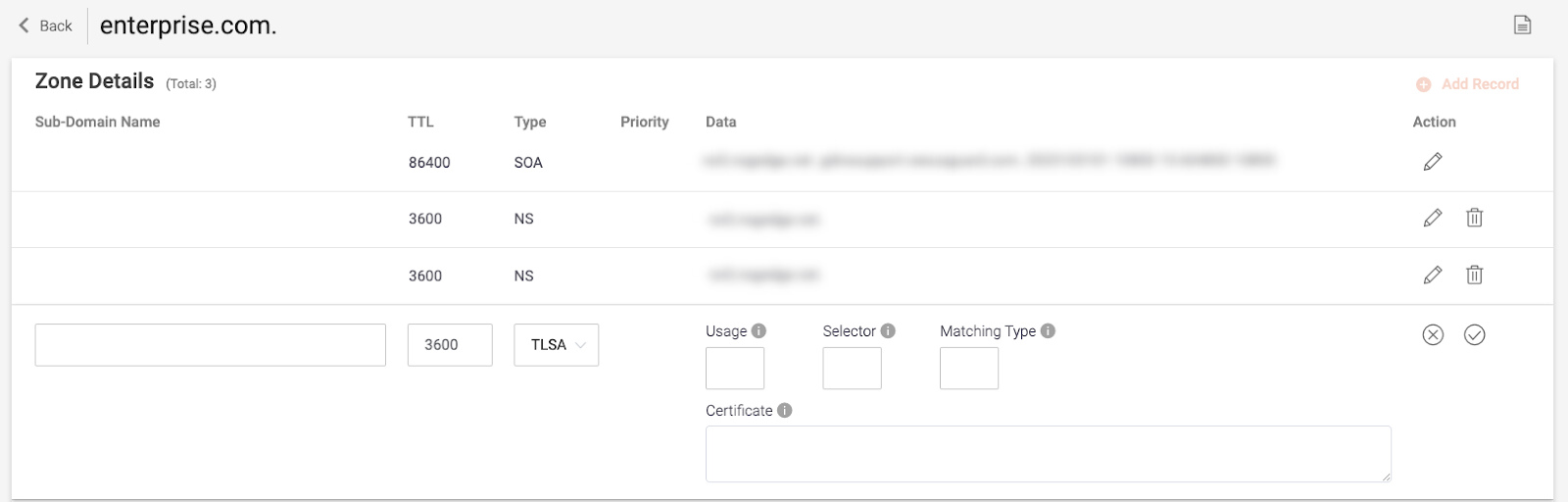
The TLS certificate information is stored within DNS records, specifically in the TLSA (Transport Layer Security Authentication) resource records. These records contain cryptographic hashes or the entire certificate itself, along with associated parameters such as the certificate usage and selector.

When a client connects to a server protected by DANE, it retrieves the TLSA records from the DNS for the domain it intends to connect to. The client then verifies the received TLSA information against the presented server certificate during the TLS handshake. If the certificate matches the TLSA records, the client can establish trust and proceed with the secure connection.
Expanding the Horizon of DANE
Within the Domain of Secure Communication, ongoing efforts have been dedicated to expanding the capabilities of authentication methods. By bridging a crucial gap in the current specification, the advancement of DANE extends beyond its primary support for TLS server certificates. This advancement now enables the authentication of TLS client certificates, opening the door to a wide array of applications that heavily rely on client certificates. Notably, the integration of DANE holds tremendous potential for Internet of Things (IoT) design patterns. In this context, large networks of domain-identified physical objects can utilize TLS to authenticate themselves, paving the way for centralized device management and control platforms.
Nexusguard DNS Protection Service Enhanced with DANE Support
Nexusguard has recently integrated DANE support into its DNS Protection Service, allowing users to benefit from enhanced security measures. With DANE support, Nexusguard ensures that SSL/TLS certificates used in hosting environments are validated and authenticated through the DNS records associated with the respective domains. This helps to mitigate the risks associated with certificate impersonation, man-in-the-middle attacks, and other types of certificate-related vulnerabilities.
For more details on Nexusguard’s range of DDoS protection services, please click here, or click here to talk with one of our experts.
Protect Your Infrastructure Today












