
Application Protection (AP)
Comprehensive Security for Public-facing Websites, Applications and Critical Web Assets

How it works
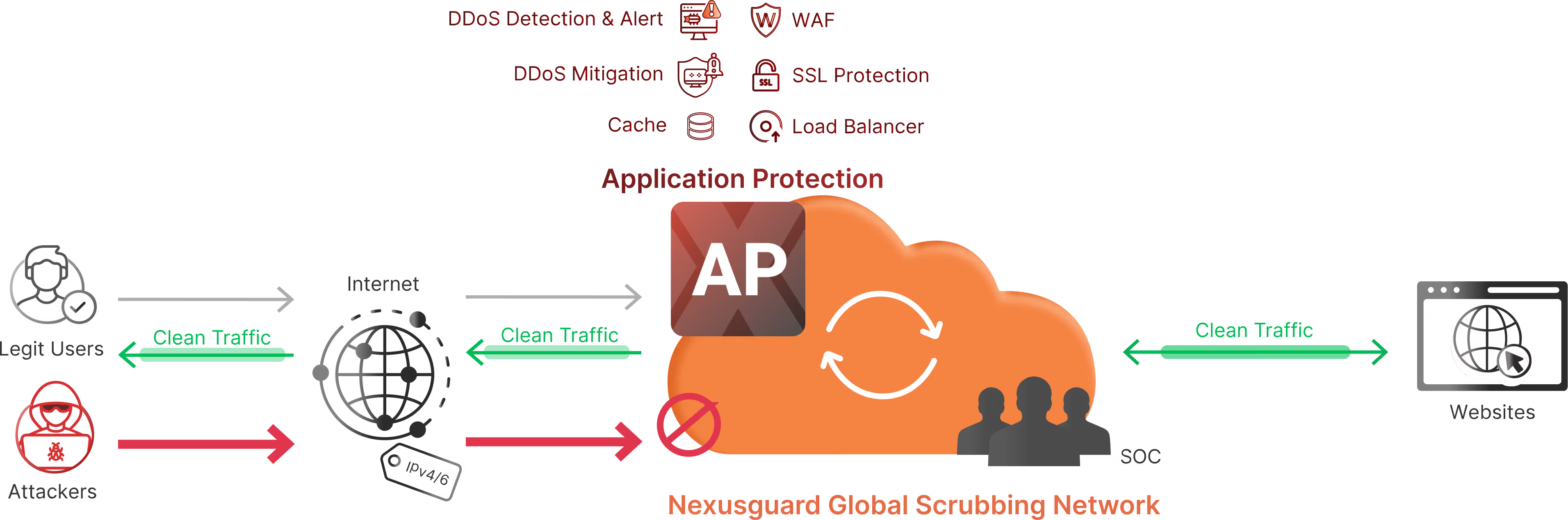
Nexusguard's Application Protection offers a strategic and comprehensive solution to safeguard your servers, and online assets. At its core, the system focuses on robust DDoS mitigation, designed to swiftly detect, intercept, and neutralize attacks before they can disrupt your websites or servers. By effectively mitigating volumetric threats and filtering out malicious traffic, Nexusguard ensures your server or application remains resilient and operational, even in the face of cyber attacks.
Once DDoS threats are successfully mitigated, Nexusguard’s Web Application Firewall (WAF) steps in as the second line of defense. The WAF proactively identifies and eliminates potential web application threats, such as SQL injection, cross-site scripting (XSS), and other vulnerabilities. This dynamic combination of DDoS protection and WAF capabilities provides organizations with a multi-layered defense against both network-level and application-level attacks.
Essential Features for Total Application Security

Always-On DDoS Protection
Safeguards websites and TCP applications from the largest application-layer and volumetric DDoS attacks using leading-edge DDoS attack mitigation techniques

Always-On WAF Protection
Protects web applications, mobile apps, and API endpoints against the most critical threats, including the OWASP Top 10

Web Optimization
Enjoy improved download speeds through caching, while reducing strain on your origin server. Combined with geolocation optimization, traffic is seamlessly routed to the nearest scrubbing center, minimizing latency and ensuring a faster, more responsive experience for users

Integrated Web & Security Analytics
Combines peacetime web analytics — offering insights into user behavior and traffic patterns — with detailed attack statistics to provide a holistic view of web activity and security incidents. Accessible via a user-friendly portal and summarized in monthly reports, it ensures consistent visibility and actionable insights for clients
Transformative Benefits for Resilient Applications
Always-on Reliability
Online Resilience
Comprehensive Protection
Traffic Visibility
Enterprise-grade Delivery
SSL Security

FAQs
Features
DDoS Detection
Nexusguard’s NetShield DDoS Module defends against Layer 3 volumetric attacks, which overwhelm networks with massive traffic floods. Equipped with advanced filters, it enables SOCs to detect, analyze, and neutralize threats in real-time. Features such as time and threshold-based detection allow precise attack identification, while peacetime autobaselining establishes baselines from network traffic patterns to simplify anomaly detection. Per-host detection ensures granular monitoring of every device, providing full visibility and control over the network.
Network Threat Intelligence Feed (NTIF) Module: Complementing NetShield is the NTIF Module, powered by a dynamic IP reputation database. NTIF tracks malicious IPs and alerts against potential DDoS threats based on their historical behavior and risk profiles, adding an intelligence-driven layer of protection.
Nexusguard’s WebShield activates after L3/L4 NetShield protection, delivering always-on security for HTTP/S traffic. Designed to defend against Layer 7 and resource-intensive attacks that specifically target websites, it ensures uninterrupted performance and reliability.
WebShield operates with independent detection and mitigation policies, allowing for precise and flexible defense mechanisms. The detection policy defines Layer 7 conditions to identify and trigger alerts for potential application-based DDoS events as soon as an attack begins. This proactive approach ensures rapid response and robust protection, keeping websites secure and operational.
Nexusguard’s Event Notifier App ensures timely awareness by delivering real-time alerts through email, SNMP Trap, or syslog. Featuring customizable alert levels, it enables proactive incident management, allowing for swift and effective responses to potential threats.
DDoS Mitigation
NetShield leverages advanced DDoS mitigation techniques to defend against L3/L4 attacks. Its key features include:
- Anti-Flooding Protection: A sophisticated set of rules combats a variety of flood attacks, such as IP, TCP, UDP, ICMP, SYN, SSL/TLS, and SIP floods. These attacks overwhelm systems by flooding them with excessive requests, depleting resources and disrupting legitimate traffic. By filtering out malicious traffic, systems remain operational and secure.
- Traffic Policing: To maintain network stability, predefined traffic thresholds are enforced after mitigation, ensuring only manageable volumes of data are forwarded to other systems or networks. This prevents tunnel congestion and minimizes disruptions across interconnected environments.
- Network Threat Intelligence Feed (NTIF): An IP reputation database identifies and blocks malicious IP addresses based on their historical behavior and risk profiles, stopping threats well before they can impact critical infrastructure.
WebShield crafts advanced L7 mitigation policies designed to block and mitigate DDoS threats effectively. Key features include:
- HTTP Authentication: Suspicious requests are routed through Nexusguard’s intelligent HTTP authentication engine, which employs a sophisticated three-layered filtering system. The authentication level can be configured as low, medium, or high, or set to operate fully automated for seamless, adaptive protection.
- Slow Attack Protection: This policy operates in three distinct modes to detect and block abnormally slow HTTP requests, preventing attackers from exploiting slow-rate techniques to disrupt services.
- RangeAmp Attack Protection: WebShield tackles invalid requests that abuse HTTP range attributes, often used to manipulate CDN servers into amplifying traffic and overwhelming target sites. By neutralizing these exploits, WebShield ensures servers remain resilient against such sophisticated attacks.
Web Application Firewall (WAF)
Nexusguard’s Web Application Firewall (WAF) utilizes advanced blocklist rules to mitigate known security threats, with a strong focus on addressing the OWASP Top 10 Most Critical Web Application Security Risks. Additionally, the WAF enhances web application security by implementing Secure Headers, which add an extra layer of protection, and CSRF tokens to ensure that HTTP requests originate from trusted domains.
Web Optimization
Our Content & Network Optimization feature delivers exceptional performance by intelligently compressing and caching all cloud-routed traffic. This dramatically enhances the speed and efficiency of high-traffic websites and online services, offering users around the world a smooth and responsive experience.
Complementing this, our advanced load-sharing traffic services evenly distribute workloads across multiple backend configurations, maximizing resource efficiency and performance. To further enhance reliability, automatic backend failover seamlessly redirects traffic in the event of a server failure, reducing downtime and guaranteeing uninterrupted access for users.
Smart Route, available as an optional enhancement to our AP service, is a sophisticated geolocation routing feature designed to enhance the experience for website visitors worldwide. By intelligently directing user traffic to strategically positioned Nexusguard scrubbing centers, it reduces latency, boosts reliability, and ensures consistent availability, delivering a seamless and responsive experience for users, no matter their location.
Web Analytics & Reporting
Nexusguard integrates web analytics and attack reporting to provide a holistic view of peacetime web activity and attack statistics. Peacetime analytics offer insights into user behavior, traffic patterns, and performance, while attack statistics analyze the nature, frequency, and impact of incidents. Both sets of data are accessible via a user-friendly portal and summarized in monthly reports, ensuring consistent visibility for clients.
Logging
Nexusguard Logger acts as a centralized repository for all log data, efficiently storing essential information such as TCP, WAF, and Web Access logs. Historical log files are readily available for download, ensuring operational transparency and compliance with regulatory standards.
Customer Portal
Designed to provide complete visibility and control, the Customer Portal is a powerful, user-friendly platform for managing security and performance. Featuring an integrated dashboard and detailed analytics, it enables customers to view and configure detection and mitigation settings tailored to their specific service plans. From monitoring real-time traffic — including raw and clean bandwidth — to tracking network performance metrics like cached bandwidth and request volumes, the portal offers a comprehensive overview of their digital environment.
Customers can stay ahead of threats by viewing ongoing and stopped DDoS attacks, analyzing potential risks, and exploring detailed insights such as visitor geography, source IPs, connection speeds, and more. The portal also provides access to detailed event logs, downloadable raw logs, and monthly reports for deeper analysis.
Resources
Datasheet
Nexusguard Application Protection Datasheet
Nexusguard Application Protection Datasheet
Whitepaper
Multi-layered Protection for Public-facing Websites, Applications and Critical Web Assets
We explore the extensive features and capabilities offered by Nexusguard's Application Protection service, specifically designed to protect public-facing websites, applications, APIs, and other critical web assets.
The Cost of DDoS Security
Nexusguard identifies and breaks down the direct and indirect capital and operations costs involved in deploying and maintaining a DDoS detection and mitigation strategy that works.
How Can Governments & Public Institutions Defend Against DDoS Attacks
Protect government and public services from crippling DDoS attacks with this whitepaper on threat impact and 360° mitigation for always‑on citizen services.
Solution Guide: Financial Services Industry & DDoS Attacks
This paper looks at how the Financial Services Industry is adversely impacted by DDoS Attacks. We present a business impact analysis and various solutions to the problems faced by the industry. The paper highlights Nexusguard’s protection suites for Applications and DNS.
Surviving GDPR Means Success in New Internet Era
To survive the GDPR data rules, businesses must prepare themselves with technology that can defend them against data breach, intrusion and service disruption.
Blog
Looking for Simpler DDoS Protection?














.avif)

.avif)

.avif)

.avif)

.avif)









