
Edge Protection (EP)
Access Your Free Virtual Demo
Why Nexusguard?
Secure Your Spot Now
Integrated Edge Protection for Resilient Uplink Connectivity

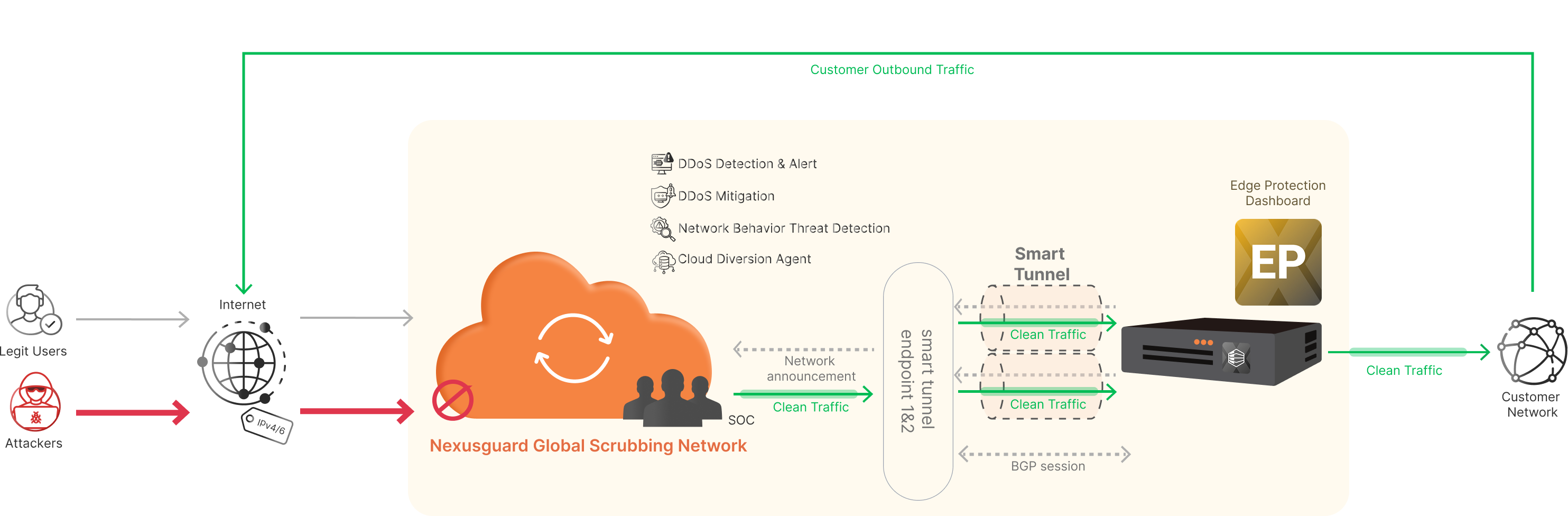
How it works
When an attack threatens to surpass local scrubbing capabilities, Nexusguard Edge Protection activates immediately to safeguard CSP partners’ uplinks. The attack traffic is scrubbed within Nexusguard’s global cloud infrastructure, neutralizing threats close to their source instantly. Meanwhile, legitimate traffic is efficiently routed back to the destination network via a GRE tunnel, enabled by the locally deployed Bastions.
Advanced Features for Edge Security

Safeguard against Volumetric Attacks
Actively protects uplink Internet connections of partner CSPs from L3-L4 DDoS attacks

Automated Traffic Diversion
Dynamically swings traffic to global scrubbing centers via Nexusguard Cloud Diversion App when attacks exceed allocated bandwidth capacity

Surgical Mitigation
Automatically removes attack traffic while ensuring the flow of legitimate traffic is uninterrupted

Flow Data Analysis Capability
Advanced multi-layered detection engine that identifies traffic anomalies through deep data analysis

Clean Traffic Delivery
After scrubbing, clean traffic is routed back to destination networks via Smart GRE tunnels terminated at the local Bastions servers
Operational Advantages for Reliable Uplink Protection
Immediate Mitigation Capacity Boost
Lowers Dependency on CSP Bandwidth
Cloud Diversion App Implementation
Attack Risk Diversion
Enhanced Attack Event Transparency

FAQs
Nexusguard's Edge Protection service stands out through its seamless integration of on-premise and cloud security, offering superior connectivity, comprehensive threat protection, and tailored solutions for diverse network environments.
Features
DDoS Protection
A robust set of rules designed to counter flood attacks, including IP, TCP, UDP, ICMP, SSL/TLS, and SIP floods. These attacks overwhelm systems by flooding them with excessive requests, depleting resources and blocking legitimate traffic. Anti-flooding ensures systems remain responsive and operational.
Powered by a dynamic IP reputation database, NTIF policies block threats based on the historical behavior and risk profiles of malicious IP addresses. This intelligence-driven approach proactively prevents attacks before they can disrupt operations or compromise security.
A highly customizable tool that defines mitigation policies tailored to customer network traffic patterns and security needs. Flex Filter goes beyond standard anti-flood measures by offering enhanced metrics and comprehensive data visualization.
This technique sets traffic thresholds post-mitigation, ensuring controlled data flow before sending it to other systems or networks. Acting as a safeguard, it prevents network congestion and minimizes disruptions across shared network resources.
SmartFilter is a cutting-edge mitigation tool within NetShield, powered by Nexusguard’s Smart Detection mode. It automatically generates and adapts mitigation rules in real-time, dynamically responding to evolving attack strategies to ensure optimal protection.
At its core, SmartFilter employs a smart feedback mechanism, which continuously monitors traffic against a clean traffic level baseline, applying mitigation actions when deviations occur. During attacks, it self-adjusts — dropping malicious traffic or allowing legitimate traffic to flow — ensuring optimal performance and robust security at all times.
Flexible Detection Modes
Continuously monitors traffic, offering advanced warnings and triggering responses if thresholds are exceeded within a set timeframe.
Focuses on bursty traffic and hit-and-run attacks, enabling quick threat detection through active traffic monitoring.
Uses Nexusguard’s AI-driven Deep Learning system for dynamic traffic profiles, ensuring precise detection and minimizing false positives.
Baselining
Leveraging advanced deep learning, Smart Baselining continuously analyzes network traffic to establish accurate baseline thresholds. This intelligent approach minimizes false alarms, enhances the speed of anomaly detection, and enables rapid threat mitigation.
Traffic Diversion
Nexusguard’s Edge Protection module leverages a Cloud Diversion App to automatically redirect customer traffic — within minutes — when it exceeds predefined bandwidth thresholds. This fully automated solution eliminates the need for on-premise hardware or manual intervention, delivering seamless, uninterrupted protection against attacks.
Administration Portal
Nexusguard’s Administration Portal is a centralized command hub for real-time security management and network performance optimization. Designed for ease and precision, its integrated dashboard provides instant visibility into traffic patterns — including raw and clean bandwidth, cached requests, and active threats — allowing teams to swiftly configure mitigation settings aligned with their service plans.
Beyond real-time monitoring, the portal delivers deep insights into ongoing and historical DDoS attacks, revealing attack sources, geolocation data, and connection anomalies. For compliance and analysis, customers can access granular event logs, export raw data, and generate automated monthly reports — ensuring every security decision is backed by actionable intelligence.
Resources
Datasheet
Nexusguard Edge Protection Datasheet
Nexusguard Edge Protection Datasheet
Whitepaper
Empowering CSPs: Enhancing Security with Nexusguard Edge Protection
This document investigates specialized anti-DDoS solutions that can efficiently shield against a wide array of DDoS attacks, ensuring uninterrupted operations for organizations.
The Cost of DDoS Security
Nexusguard identifies and breaks down the direct and indirect capital and operations costs involved in deploying and maintaining a DDoS detection and mitigation strategy that works.
A New Threat to CSP Networks – The Impending “Black Storm"
Nexusguard Research Team recently theorized that a cyber threat, coined the “Black Storm” attack, could potentially be used by attackers to wreak havoc on CSP (Communications Service Provider) networks.
Surviving GDPR Means Success in New Internet Era
To survive the GDPR data rules, businesses must prepare themselves with technology that can defend them against data breach, intrusion and service disruption.
Looking for Simpler DDoS Protection?














.avif)

.avif)

.avif)

.avif)

.avif)




