Safeguard your internet uplink and network infrastructure with Nexusguard Origin Protection

Nexusguard

Share to:
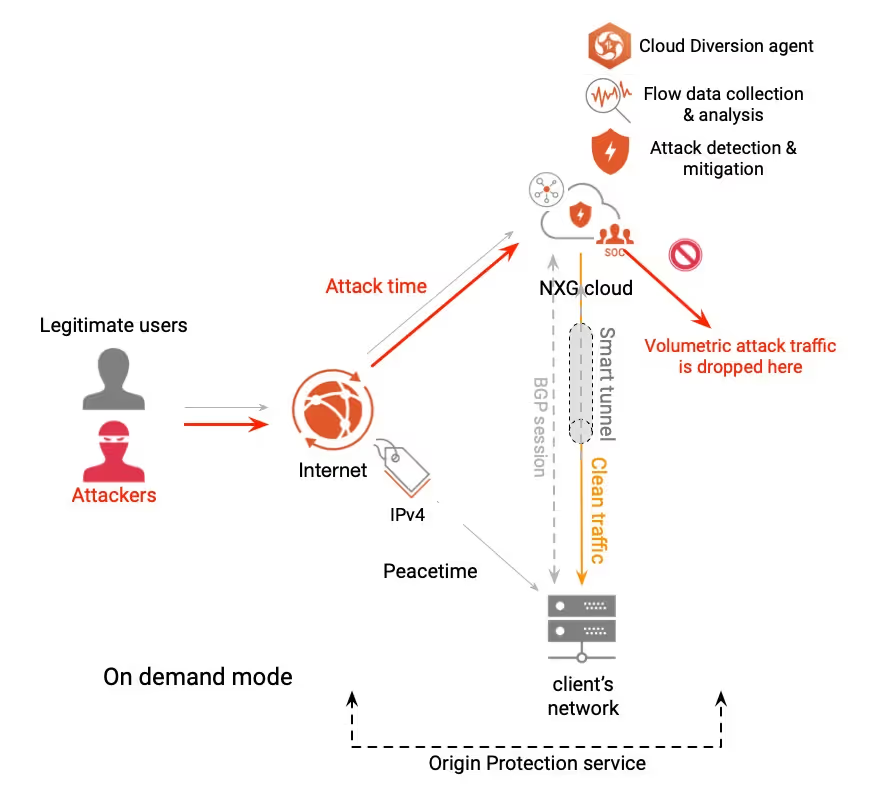
Nexusguard's Origin Protection stands at the forefront as an advanced, on-demand managed service explicitly designed to safeguard mission-critical services across large networks, offering robust protection against L3/4 and various L7 attacks. Origin Protection caters not only to Nexusguard's direct clients but also to clients directly connected to partner CSPs that have deployed Nexusguard Bastions.
The primary objective of Origin Protection revolves around maximizing subscribed Internet access availability to its fullest potential, relieving the network from the burden of junk traffic stemming from volumetric DDoS attacks. Through the efficient filtration of superfluous and malicious data, this service guarantees uninterrupted network availability, facilitating seamless utilization of resources. Consequently, users can revel in fast and reliable connectivity, undisturbed by harmful traffic attempting to disrupt their online activities.
Origin Protection Service Scope
Origin Protection safeguards IPv4 addresses against all volumetric and protocol-based DDoS attacks, such as UDP, SMTP and SYN floods, ensuring uninterrupted connectivity.
Through the employment of advanced flow data collection and analysis techniques, Nexusguard's Origin Protection enables the prompt detection of potential DDoS attacks, ensuring swift and decisive action can be taken. Additionally, the service provides a Cloud Diversion App that automatically diverts IP prefixes under attack, guaranteeing that these targeted addresses are swiftly redirected to a secure environment. This intelligent diversion ensures that critical services remain accessible to legitimate users, while efficiently mitigating the impact of DDoS attacks in real-time, preventing access network congestion.
Upon successfully neutralizing threats, Origin Protection ensures the return of clean traffic to networks through diverse L2-type connections. These connections, such as DC (Direct Connect), GRE (Generic Routing Encapsulation), and VPLS (Virtual Private LAN Service), are deployed based on specific needs and considerations of network connectivity. Nexusguard's secure and efficient traffic delivery mechanism ensures uninterrupted accessibility and functionality of client networks, safeguarding against disruptions caused by malicious activities.
Prerequisites for Enabling Origin Protection
To ensure successful implementation of Origin Protection, the following prerequisites must be met:
1. Internet Routable /24 Prefixes
To enable Origin Protection, the protected IP address range must be Internet routable /24 prefixes. This requirement ensures that the protected IP range can be effectively managed and secured using the service.
2. Control of Routing Policy
Together with its own AS number, the Origin Protection Client must possess total control over the routing policy. This level of control allows the client to independently manage their routing domain and make necessary adjustments for optimal security and performance.
3. Ability to Establish BGP Connections
In addition, the Origin Protection Client must have the capability to actively participate in BGP routing exchanges in order to allow for smooth communication and collaboration with other networks, thereby enhancing the security and reliability of the protected IP range.
Flexible Protection Profiles
Origin Protection provides complete L3/4 protection for clients’ subscribed IP prefixes, ensuring that all network resources associated with these IP prefixes are protected against DDoS attacks.
Origin Protection offers the flexibility to segregate a client's network address space, which may consist of multiple Class C networks, into distinct protection profiles. This allows for customized protection based on factors such as importance of service, specific needs, and usage requirements, providing dedicated defense against DDoS attacks. It should be noted that the segregation of protection profiles must align with the network boundary of a routable Class C network. This ensures efficient and targeted protection for different segments of the network, enhancing overall security and resilience.
Furthermore, grouping of IP Prefixes based on similar usage or traffic profiles also allows the service to apply targeted protection measures to each group, optimizing defense strategies and ensuring efficient utilization of resources.
Benefits of Origin Protection
Implementing Origin Protection offers a range of advantages and benefits, as detailed below:
Origin Protection takes a proactive approach in minimizing collateral damage by strategically shifting frequently attacked IPs away from the main uplink. This transfer of security risk to the DDoS protection provider allows them to handle and mitigate the attacks more effectively. To ensure this, Origin Protection ensures that peacetime and under-attack IPs flow through separate Internet uplinks. By implementing this, the network quality of unaffected networks is preserved, ensuring that it remains at the same level as during peacetime. This approach not only safeguards network performance but also effectively manages and mitigates the impact of attacks, providing a more resilient and secure network environment.
The benefits of Origin Protection exceed its primary security function, offering unparalleled advantages in maximizing network availability and mitigating congestion on the Internet uplink caused by volumetric attacks. Clients experience uninterrupted connectivity, enabling smooth operations even during volumetric attacks.
Another key benefit of Origin Protection is the provision of the Cloud Diversion App. This app automatically diverts IP prefixes that come under attack, swiftly redirecting them to a secure environment, ensuring that critical services remain accessible to legitimate users, even during a DDoS attack. By automating the diversion of under attack traffic, Origin Protection eliminates the need for manual route updates, mitigating the risk of human errors. This streamlined process not only enhances operational efficiency but also ensures a seamless and error-free experience, allowing organizations to focus on their core tasks with peace of mind.
Protect Your Infrastructure Today












