Beyond VAPT: Why DDoS Simulation Is the Missing Piece of Cyber Resilience


Donny Chong
Nexusguard

Share to:
Every organization that operates online lives with the constant risk of a Distributed Denial of Service (DDoS) attack. It is one of the few cyber threats that does not need to exploit a vulnerability. It simply overwhelms everything in its path.
Despite years of investment in cybersecurity testing, most enterprises and service providers have never actually tested what would happen if they were attacked. Vulnerability Assessment and Penetration Testing (VAPT) remains a cornerstone of good security hygiene, but it stops short of validating one crucial question: can your systems stay online when traffic turns hostile?
The Problem: The Blind Spot in Traditional Testing
Traditional VAPT focuses on software and configuration weaknesses such as unpatched systems, exposed endpoints, or insecure coding practices. A DDoS attack is different. It is not trying to break in. It is trying to break down capacity.
When upstream links saturate, when DNS servers become overworked, or when application stacks are forced into resource exhaustion, the result is identical to a successful breach: downtime, disruption, and customer-impacting outages.
Yet these scenarios are almost never simulated in conventional penetration tests. The result is an untested assumption of resilience that only holds until the day it is proven wrong.
Our Approach: From Internal Tool to Industry Service
To continuously improve our own global scrubbing infrastructure, Nexusguard built an internal DDoS simulation platform capable of safely generating large-scale attack traffic across multiple layers and geographies.
Originally used to validate detection logic, train SOC analysts, and support complex partner testing, this internal capability evolved into the Nexusguard DDoS Simulation Service. It is a controlled and fully managed environment designed to help organizations run credible, high-fidelity attack scenarios without risk to the public Internet.
The Difference: Real Resources, Real Scale, and Real Control
A meaningful DDoS simulation is very different from a traditional penetration test.
Where VAPT can be executed from a handful of laptops, virtual machines, or small cloud instances, a realistic DDoS simulation demands a far greater level of scale and sophistication. It calls for:
- Large bandwidth reserves
- Distributed global IP sources
- Numerous traffic generation agents
- Specialized protocol and packet behavior tools
- High-performance compute and routing capacity
- Centralized orchestration with strict control mechanism
These capabilities allow the simulation to mirror real-world attacks rather than simplified or synthetic approximations.
However, raw capability alone is not enough. Without strict oversight, this level of power can be dangerous. Every simulation must be executed with precision and discipline. Nexusguard’s strength lies in the fact that simulations are designed and supervised by practitioners who mitigate live DDoS attacks every day. They understand attack behavior, escalation triggers, and the safety boundaries required to prevent unintended disruption.
Power without control creates risk. Nexusguard brings both power and control together.
How It Works: Controlled Chaos, Safely Executed
Nexusguard’s DDoS Simulation Service launches distributed test scenarios from multiple global regions and scrubbing centers. These scenarios reproduce the traffic patterns used by modern attackers without impacting the public Internet or unrelated systems.
Every simulation begins with careful planning. The organization defines the type of test, the environment to be evaluated, and the targets involved. Timing is precise because high-volume traffic cannot be allowed to overlap across conflicting schedules. Targets may be drawn from predefined safe environments or provided as custom endpoints that require authorization before testing begins.
Once initiated, the simulation runs the selected attack vectors at the chosen intensities. Depending on the objective, a test may last for a short interval or run for several hours to measure stability under sustained pressure. When the exercise finishes, detailed data is collected across all relevant layers to evaluate system behavior, mitigation performance, and potential gaps.
Flexible Single-Vector or Multi-Vector Scenarios
A key strength of Nexusguard’s simulation service is the ability to shape traffic in ways that reflect real attacker behavior. Threats differ across industries, regions, and infrastructure types. The platform supports a wide range of scenarios, from simple single-vector conditions to complex multi-vector sequences.
A Wide Library of Real Attack Types
Not all DDoS traffic behaves the same. Some attacks rely on raw volume. Others exploit protocol quirks or overwhelm specific application functions. To reflect this diversity, Nexusguard’s simulation platform includes hundreds of attack types derived from real incidents, global threat intelligence, and research analysis.
This extensive library allows organizations to select the exact vectors they want to test, whether they are validating baseline controls or recreating attack patterns seen in their region or industry.
This is only a small portion of what the platform can generate. The full library contains many more variations in packet profiles, payload sizes, source characteristics, and amplification behaviors, making each simulation as realistic as possible.
Single-Vector Attacks
Single-vector simulations focus on one type of traffic to study its direct effect. Examples include:
- A pure TCP SYN flood
- A DNS request surge
- An amplification vector such as NTP or SSDP
These tests help teams isolate specific weaknesses and fine-tune detection rules and infrastructure settings.
Multi-Vector Blended Attacks
More sophisticated attackers combine several techniques in a single campaign. A blended simulation can mirror this behavior by introducing multiple attack vectors at once.
A blended scenario may include:
- A volumetric flood to saturate bandwidth
- Protocol anomalies to destabilize routers or firewalls
- Application request bursts to overwhelm web or API services
This coordinated pressure exposes vulnerabilities that would not emerge in isolated tests.
Custom Composite Scenarios
Some organizations require tailored scenarios based on their specific risk profile or industry requirements. Custom composite simulations can replicate:
- Region-specific botnet behavior
- Known attack patterns observed globally
- Compliance-driven testing requirements
- Unique conditions tied to the organization’s environment
This flexibility ensures the simulation matches real-world threats as closely as possible.
Use Cases: Testing That Delivers Real Value
Organizations rely on Nexusguard’s DDoS Simulation Service for scenarios such as:
- Pre-production validation of Bastions, Clean Pipe, and Origin Protection deployments
- Proof-of-concept demonstrations for customers or regulators
- SOC readiness drills using realistic traffic
- Compliance-driven resilience testing
- Incident response rehearsals to strengthen coordination under pressure
Each simulation demonstrates how defenses behaved, where safeguards held firm, and where tuning may be needed.
Post-Simulation Reporting: Turning Data Into Action
A DDoS simulation is only as valuable as the insight it produces. For this reason, every Nexusguard exercise concludes with a structured after-action review that translates raw traffic data into clear operational findings.
Reports include:
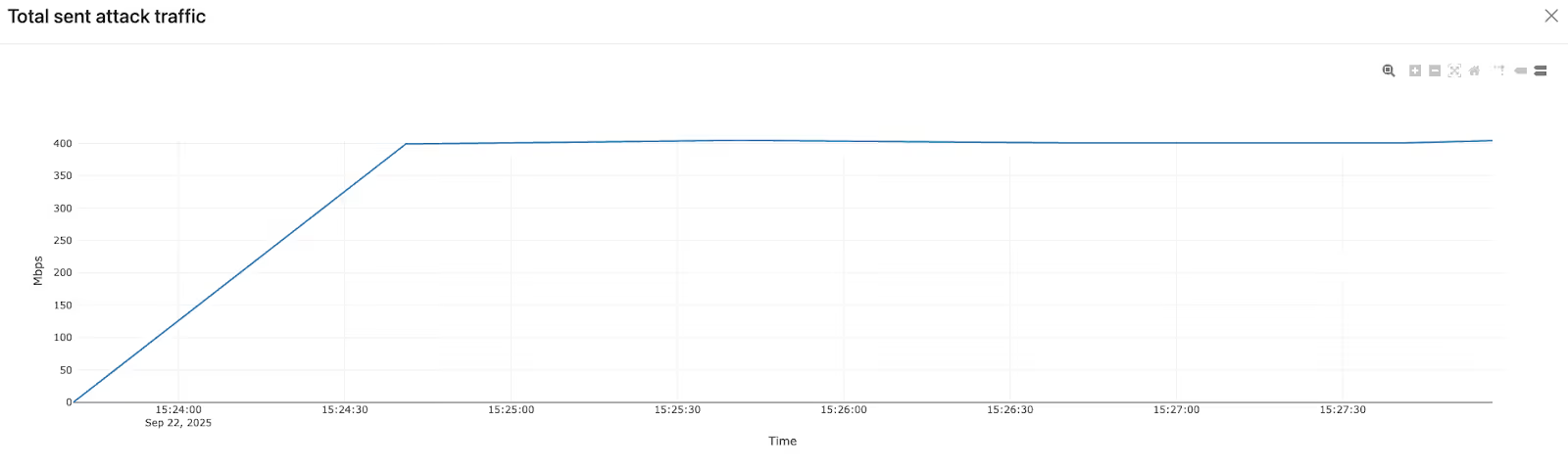
- Traffic graphs showing how attack volume ramped up, peaked, and stabilized
- Packet rate and bit rate analysis across the full duration
- Breakdown of traffic by attack group to understand vector-specific behavior
- Key performance indicators such as peak, average, and minimum attack size
- A precise timeline documenting test duration and system stability
- A written summary outlining observations and recommendations
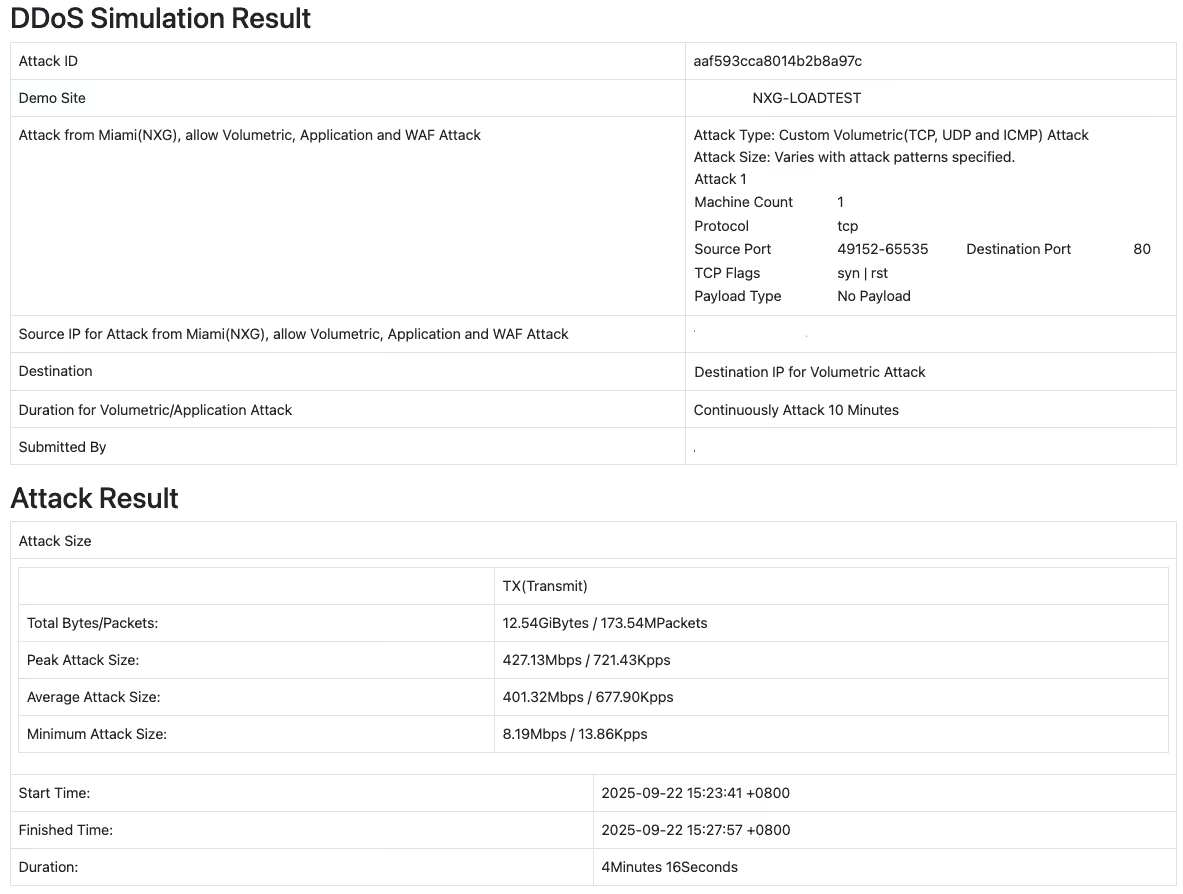
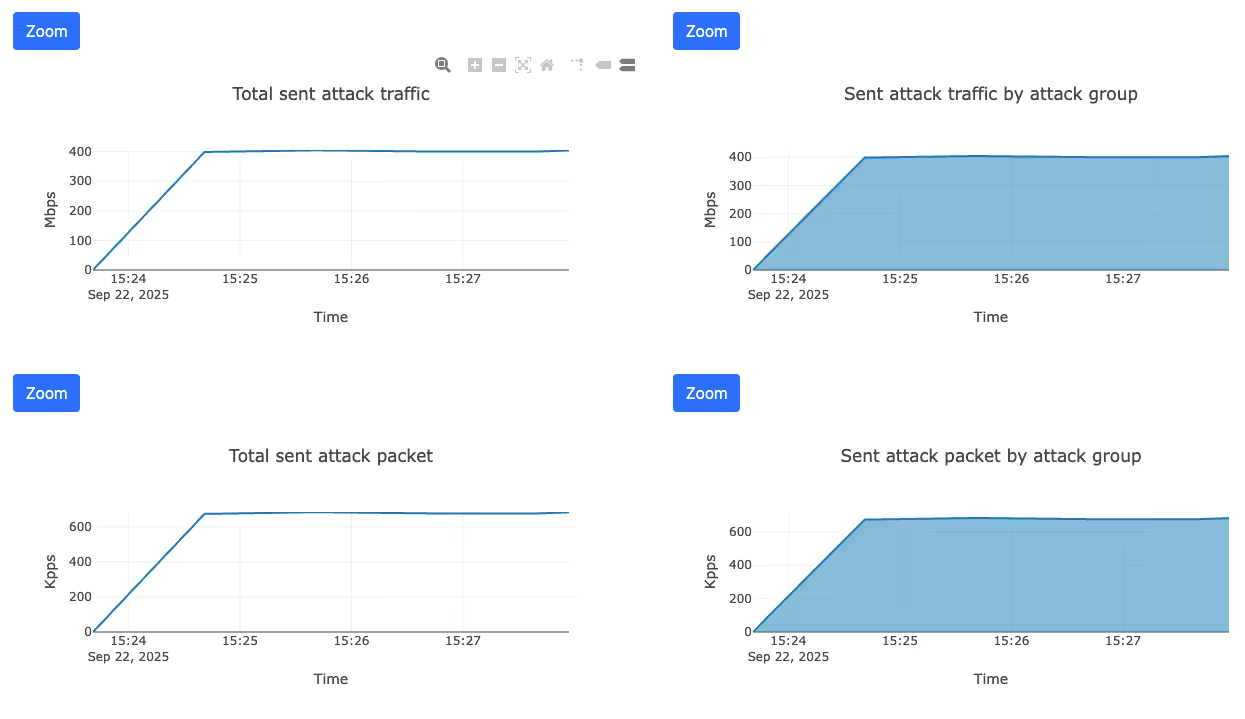
These insights help teams understand exactly how their systems performed and what actions can strengthen resilience.
Why It’s Different
- Simulations run entirely within Nexusguard’s controlled infrastructure
- Attack variety reflects real-world behavior, not theoretical patterns
- The platform is powered by the same global scrubbing backbone used for production traffic
- Every scenario is guided by engineers who mitigate live DDoS attacks daily
- Customers can customize scenarios from simple to highly complex
- Reports provide insights suitable for both technical and executive audiences
The Outcome: From Assumption to Assurance
DDoS resilience cannot be assumed. It must be tested under conditions that mirror reality. Nexusguard’s DDoS Simulation Service provides a safe, controlled, high-fidelity approach to evaluating readiness and strengthening defenses.
When the next attack arrives, you will already know how your systems respond, how your teams react, and where improvements are needed. You will have faced the pressure before, and you will be prepared.
Protect Your Infrastructure Today












